2022/2023 NCSC incidents
This fiscal year we recorded 316 cyber security incidents. This figure is about 10% lower than the previous year. The difference may reflect a number of contributing factors, including: recent disruptions to cyber criminal infrastructure; changing priorities or tactics of states; organisational cyber resilience and maturity; and/or our increasing ability to disrupt activity before harm takes place. Developments in the NCSC’s cyber defensive capabilities have allowed us to scale some services to a significant number of organisations, and even to protect individual home users.
The NCSC receives information about cyber security compromises or suspicious cyber activity from a number of sources, including its own detection and discovery capabilities, international cyber security partners,
domestic agencies, and customers themselves.
Despite a drop in the total number of incidents recorded, including incidents reported to the NCSC by other organisations, the number of incidents detected by NCSC capabilities grew year-over-year. Viewed over the last four fiscal years, the number of incidents detected by NCSC capabilities accounts for about a third of our total recorded incidents.
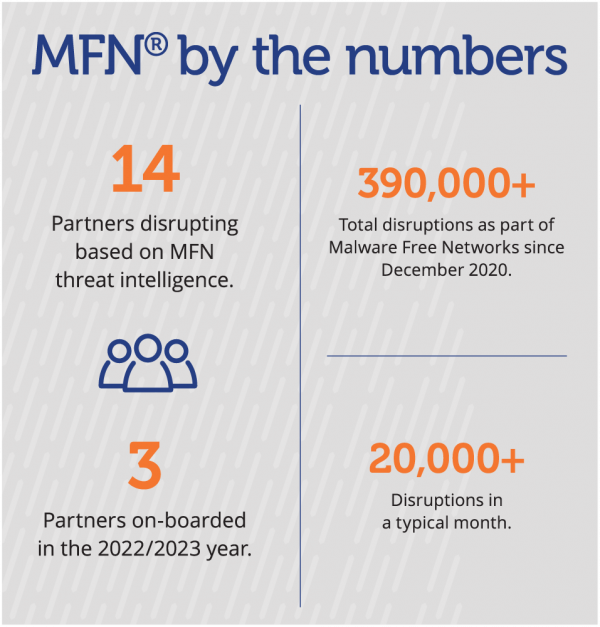
A typical month this year saw the NCSC’s MFN® service disrupting 20,800 connections to known malicious infrastructure; the NCSC detecting seven cyber incidents; and receiving 20 reports or requests for assistance. Of the incidents reported, the NCSC receives an average of 12 from domestic or international partners and eight self-reports from victim organisations themselves.
How the NCSC defines incidents
An NCSC incident can be any threat to a nationally significant organisation’s network or information – or where the activity has the potential to cause high national harm. This may occur even when an actor is unsuccessful or there is no confirmed compromise.
Reconnaissance and network scanning, possible attempts to exploit customer vulnerabilities, accidental data leaks, or suspicious events that trigger analysis to determine if they are malicious can all be counted among the NCSC’s total incidents.
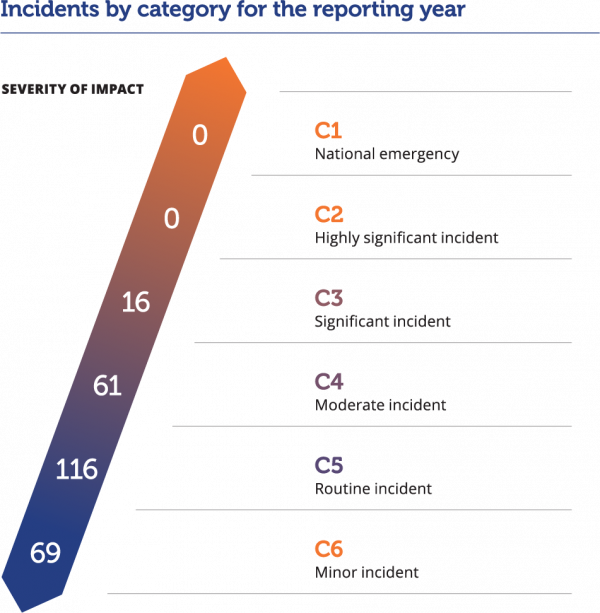
We categorise incidents by considering the scope, size, and role of the affected victim alongside the possible harm and impact caused by the incident. Incidents range from category 6, being minor or of least concern, to category 1, being critical.
What's the harm?
In 2022/2023, the detection, disruption, advisory and threat intelligence services the NCSC provides prevented an estimated $65.4 million of harm to Aotearoa New Zealand’s nationally significant organisations. This figure reflects incidents where the NCSC’s detection of malicious cyber activity or engagement with victims likely prevented future harm.
The estimate is 98% higher this year than last. This reflects the advice we gave to organisations responsible for critical services – such as power, waste, and water where cyber incidents can be more impactful – or the NCSC’s support to information technology (IT) managed service suppliers with various Aotearoa New Zealand government customers. In these cases, the compromise of one organisation could have significant downstream harms to several nationally significant organisations. Finally, in 2022/2023 the NCSC was more readily able to verify that organisations took actions in response to our advice, which is a key factor in measuring our impact.
In 2016, the NCSC commissioned independent research to devise a model that could measure the benefits provided by our interventions. The model was reviewed and updated in 2020 to ensure it better reflects international studies about the average cost of cyber security incidents to specific sectors.
The model factors in important impacts such as losses caused by intellectual property theft, including copyright and patent infringement. While assigning a dollar value to harm prevention can provide a useful benchmark, many of the impacts of cyber harm are intangible. Loss of public confidence and trust, reduced health and wellbeing, and hesitance to adopt new technologies can all eventuate when cyber resilience is low.
The pre-emptive and preventive nature of our MFN® capability means any malicious activity generally occurs at a point before its value is able to be reflected in this calculation. However, there were several instances in the 2022/2023 year where activity detected by the MFN capability was responded to as an incident. Typically, in such cases a compromise has already occurred and MFN is able to disrupt secondary effects of the compromise. Those incidents are reflected in this calculation.
The total number of incidents is only part of the story. A handful of significant incidents in a fiscal year would more radically change the domestic landscape than hundreds of minor incidents because the potential impact on critical services, society, and the economy would be greater. To help understand the impact of any one cyber incident, the NCSC triages incidents into categories, which consider the size of the organisation impacted and the severity of the compromise. A national cyber emergency (C1) is a cyber incident causing severe disruption to a core Aotearoa New Zealand service, and/or affects key sensitive data, and/or undermines the economic or democratic stability of Aotearoa New Zealand. To date, the NCSC has never responded to a C1 cyber incident. If one were to occur, it would demand a resource-intensive, multi-agency response, with the NCSC providing advice, coordination, and its technical capabilities.
On the other end of the scale, a minor incident (C6) is a cyber incident causing a known or likely impact to an individual/individuals, or precursor activity against an individual/individuals or a small or medium enterprise. During a C5 or C6 incident the NCSC may be involved in providing advice or guidance to the organisations as they triage the incident and harden their defences for the future, or we may pass the investigation to CERT NZ to provide appropriate advice.
In the middle, a significant incident (C3) is an incident causing a known or likely impact on a large commercial enterprise, wider government, or supply chain to core Aotearoa New Zealand services. Even a C3 can require significant effort on behalf of the NCSC, as well as the victim and their cyber security and IT suppliers. The initial response can last weeks. These incidents tend to have a long tail for the victim – and sometimes for their customers, too.
This year’s most severe incidents were categorised C3. Unlike the 2021/2022 year, in which we recorded two C2 incidents, the 2022/2023 C3 incidents were predominantly associated with disruptive ransomware or other extortion activity. A number of these incidents had second-order effects for Aotearoa New Zealand organisations. For instance, the compromise of one organisation posed risks to the privacy and security of a number of other Aotearoa New Zealand organisations.
Another C3 incident began with the compromise of an internet-facing device in a local government organisation. While the device was likely compromised opportunistically, owing to the availability of known vulnerabilities in a commonly used security product, the malicious cyber actor successfully moved laterally within the victim’s network. The NCSC alerted the organisation to the compromise, likely by a sophisticated malicious cyber actor seeking data for espionage purposes. Before detection and containment, the actor compromised a server and several devices belonging to the victim.
The NCSC assisted the victim organisation and its IT managed service provider to understand the scope of the intrusion, remove the intruder and prevent further attempts to compromise their network. Prompt response efforts and work to identify the full path of the intrusion contained the compromise and reduced its impact.
Incidents by category for the reporting year
Disrupting malicious cyber activity
Aotearoa New Zealand calls out malicious cyber activity when it is in the national interest to do so. By providing examples of malicious cyber activity in public, Aotearoa New Zealand can raise awareness of the threat, and signal to nation states what it views as irresponsible behaviour.
The GCSB, through the NCSC, conducts robust technical attribution of malicious cyber activity affecting our national security and wellbeing. We usually provide these as classified assessments to the Aotearoa New Zealand Government for use in an all-of-government process determining our national response.
On some occasions, malicious cyber activity affects Aotearoa New Zealand’s interests indirectly, or has the potential to affect us in future. In these circumstances, the NCSC may join international partners to produce advisories that identify malware or specific tactics, techniques and procedures (TTPs). These advisories raise awareness of the cyber threat and provide information to mitigate malicious cyber activity.
Increasingly, nation states are undeterred by a process of ‘calling out’ malicious cyber activity – in other words, being associated with malicious cyber activity. However, nations opposing the malicious use of cyber capabilities can take steps to impose real costs: providing indicators of compromise or identifying malware and behaviours to enable faster detection and incident response, thereby reducing the effectiveness of malicious cyber tools and infrastructure. This can have a profound levelling effect, benefiting the defenders of critical networks and services.
During the 2022/2023 year, the NCSC contributed to several cyber security advisories, publicly identifying sophisticated malicious cyber activity and providing steps to detect and mitigate its impact.
In May 2023, we joined international cyber security partners in disclosing technical information about malware associated with Russia’s Federal Security Service (FSB) and frequently used against sensitive intelligence targets. Together with partners in Australia, Canada, the United Kingdom and the United States, the NCSC provided information about the latest revision of malware known as ‘Snake’.
In the same month, the NCSC joined its like-minded partners to identify techniques associated with the stealthy compromise of critical infrastructure. By ‘living off the land’ sophisticated cyber actors from the PRC were able to use legitimate tools existing on victim devices and networks to maintain access to significant overseas targets without detection.
In June 2023, the NCSC and partners identified tactics associated with the deployment of LockBit – the most pervasive ransomware worldwide, and with significant impacts in Aotearoa New Zealand. LockBit has affected government, energy, emergency services, healthcare and logistics sectors internationally. The advisory Understanding Ransomware Threat Actors: LockBit identifies the legitimate re-purposed tools and the MITRE ATT&CK® TTPs associated with LockBit actors.
In each of these cases, the NCSC supported the distribution of threat information – including through its co-chairing of Security Information Exchanges.
Another key way we disrupt malicious cyber activity affecting Aotearoa New Zealand is through the provision of the MFN® threat detection and disruption service. In the 2021/2022 year, the NCSC launched the service, working with commercial cyber security and infrastructure partners to provide high confidence malicious indicators that should be disrupted wherever they are detected.
With 14 industry partners offering MFN to their customers, including three new partners this fiscal year, 2022/2023 demonstrated the scalability of our defensive capabilities, with over 250,000 disruptions, including hundreds of disruptions associated with state-sponsored activity. As of 30 June 2023, MFN had disrupted more than 390,000 threats in total. This figure reflects disruptions of malicious activity with the potential to cause harm to Aotearoa New Zealand organisations and individuals.
Through MFN, the NCSC also supplied cyber defenders with indicators for a number of unique threats to Aotearoa New Zealand, including the impersonation of Aotearoa New Zealand organisations and government services – this activity contributed to over 20,000 disruptions.
In 2022/2023, the NCSC worked with partners One NZ and DEFEND to prepare the MFN service for scaling to One NZ’s domestic broadband and mobile customers. With an increased reach of around two million people, we have provisionally observed a growth in reported disruptions of over 3,000% since June 2023.
MFN by the numbers